Why Alert Enrichment is Critical: Turning Signals into Security Knowledge

Every day, Security Operations Centers (SOCs) are inundated with alerts. These alerts come from a variety of sources — endpoint detection systems, SIEMs, firewalls, intrusion prevention systems, cloud security tools, and beyond. Yet, in their raw form, these alerts are just signals. Some might be benign. Some might be redundant. Some could be the beginning of a breach. The challenge lies in knowing which is which.
Raw alerts, without context, are like puzzle pieces with no picture to guide assembly. They lack meaning, priority, and relevance. SOC analysts, tasked with determining what matters most, are left navigating thousands of such pieces daily — many of which look alike. This is where alert enrichment becomes critical.
Alert enrichment is the process of adding meaningful context to raw alerts. It transforms a disconnected event into an actionable piece of intelligence. With proper enrichment, analysts can make better decisions faster, reduce time-to-triage, and automate large portions of incident response.

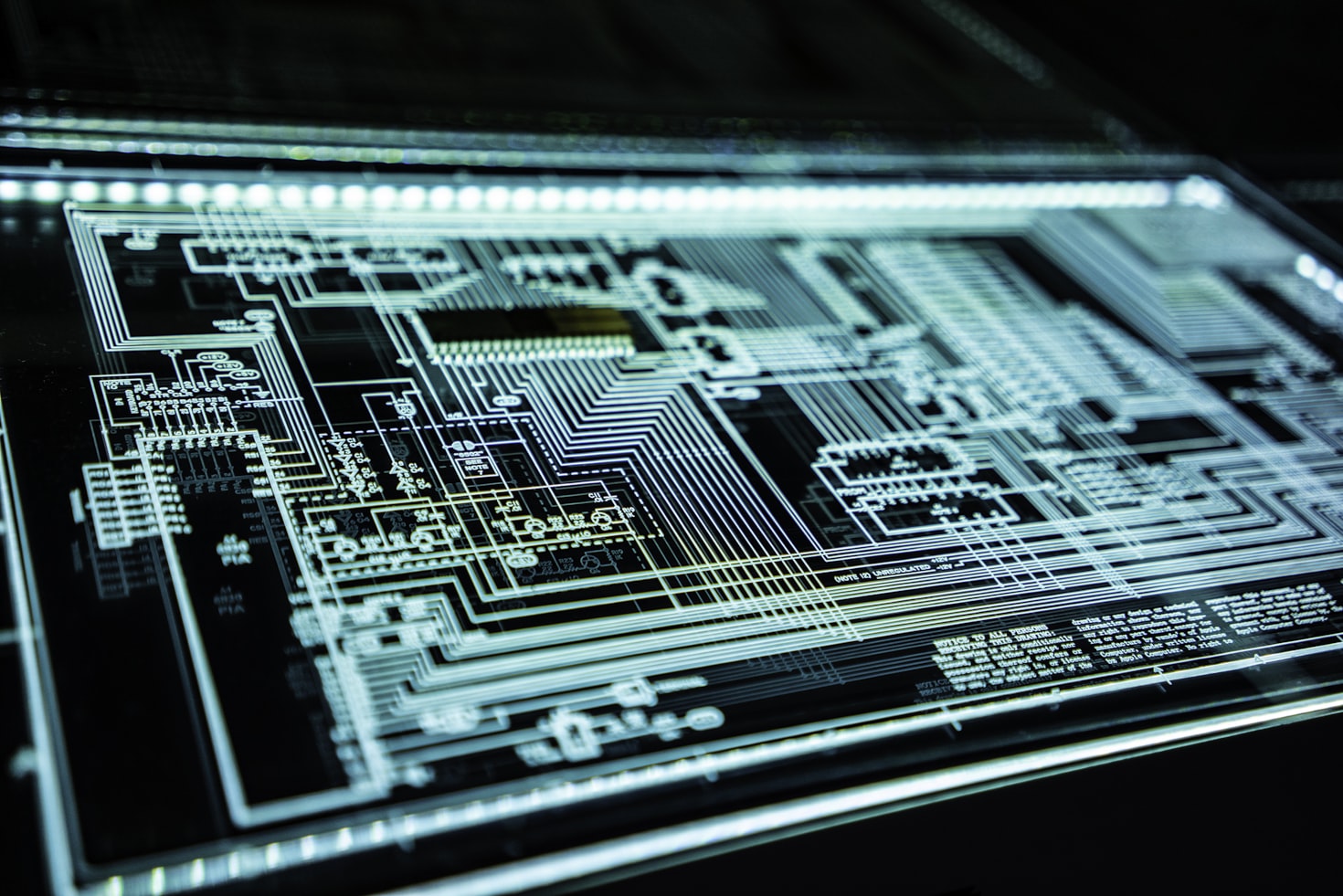
Alert enrichment transforms raw signals into actionable security intelligence with context and meaning
The Context Gap in Raw Alerts
Imagine receiving an alert that reads: "Unusual login activity from IP 172.89.43.12." What does this mean?
Without context:
- Is this IP internal or external?
- Has this user logged in from this IP before?
- Is this device considered critical or disposable?
- Is this behavior common at this time of day?
Lacking answers to these questions, the alert is meaningless — or worse, misleading. Enrichment bridges this gap. It provides the metadata and relationships that turn signals into knowledge.
A properly enriched version of this alert might say:
User 'j.doe' logged in from external IP 172.89.43.12, geolocated in Moscow, at 3:12 AM local time — outside normal working hours. This user typically logs in from London. This IP is associated with known brute-force attempts. The asset accessed is 'finance-prod-db01', classified as Tier 1 critical.Suddenly, the alert becomes actionable — and alarming.
Types of Alert Enrichment
1. Internal Enrichment
Internal enrichment sources come from within the organization. These are often highly specific to your environment and carry the most operational weight.
Geolocation
Determining the physical location of an IP address provides quick insight into whether activity is expected or suspicious. A login from a known country or office location may be benign. One from an unrecognized or high-risk country may require escalation.
Behavioral Baselines
Has this user or system performed similar actions in the past? Has a login at this hour, from this endpoint, or using this protocol occurred before? Establishing a behavioral norm allows deviations to stand out — even if they aren't obviously malicious.
Historical Alerts
Understanding the historical frequency of a particular alert type or behavior provides essential context. If this alert has triggered 200 times in the last week without consequence, it may be deprioritized — unless paired with a new behavior.
Asset Classification
Knowing what system is being impacted changes the urgency. An alert on a developer laptop is one thing. The same alert on a PCI-compliant payment gateway is quite another. Asset importance must be factored into every triage decision.
User Role and Identity
Is the user a domain admin or a temp contractor? Are they part of the finance team or customer support? Identity and access context is crucial in judging intent and risk.
Integration with CMDB
A well-maintained Configuration Management Database (CMDB) can act as a source of truth for internal enrichment. It provides relationships, ownership, system function, and lifecycle stage for any given asset.

Internal enrichment draws from organizational data sources to provide environmental context
2. External Enrichment
While internal enrichment contextualizes alerts within your environment, external enrichment provides threat intelligence and global perspective.
Threat Intelligence Feeds
These feeds include known bad IPs, URLs, domains, file hashes, and attacker tactics. If an alert references an external IP and that IP is flagged on five reputable feeds, its priority increases substantially.
CVE Mapping and Exploit Availability
If an alert relates to a known vulnerability, enrichment can add the CVE reference, severity score, affected software, and whether public exploits exist. This is critical in patch prioritization and attack surface reduction.
MITRE ATT&CK Mapping
Mapping alert behavior to known adversary tactics provides structured, adversary-focused understanding. It allows defenders to understand not just what happened, but why — and what might come next.
Geo-IP and ASN Data
These datasets inform whether external communications are unusual or associated with hostile networks. Autonomous System Numbers (ASNs) help group IPs into ISPs or hosting providers, offering additional insight into intent.
External Reputation Scores
Vendors often provide reputation scoring for entities (IP addresses, emails, domains). These scores can quickly signal whether an entity has a history of malicious activity across multiple clients and verticals.
Enrichment in Action: A Before/After Scenario
Before Enrichment
Alert: "Process launched: powershell.exe"
System: HR-laptop-223
Time: 14:42After Enrichment
Alert:
A PowerShell process was launched on endpoint 'HR-laptop-223' by user 'a.watson', who typically does not use scripting tools. The process attempted to connect to '198.51.100.25', a flagged IP in three threat intel feeds. The endpoint has not launched PowerShell in the last 90 days. User role: HR. Time of execution was during an HR sync session with sensitive PII involved.This transformation is dramatic. It turns a vague process execution into a potentially serious breach indicator. The difference lies in the data layers added through enrichment.

Enrichment transforms basic alerts into comprehensive threat intelligence with actionable context
How Enrichment Enables Prioritization
Triage decisions depend on more than the presence of a signal. They depend on urgency, relevance, and risk. Enrichment enables the SOC to assign meaningful priority scores based on a multi-dimensional view of each alert.
Factors that influence prioritization:
- Asset criticality
- User sensitivity
- Behavior novelty
- External threat matching
- Proximity to high-value data
- Sequence within a known attack pattern
Some SOCs use custom scoring algorithms. Others rely on ML models that weigh features dynamically. In both cases, enrichment provides the raw material from which intelligent prioritization is built.
# Example priority scoring algorithm
def calculate_priority_score(alert):
score = 0
# Asset criticality (0-40 points)
if alert.asset_tier == "Tier 1":
score += 40
elif alert.asset_tier == "Tier 2":
score += 25
elif alert.asset_tier == "Tier 3":
score += 10
# Threat intelligence matches (0-30 points)
score += min(alert.threat_intel_matches * 10, 30)
# Behavioral anomaly (0-20 points)
if alert.behavior_deviation > 0.8:
score += 20
elif alert.behavior_deviation > 0.5:
score += 10
# User privilege level (0-10 points)
if alert.user_role in ["admin", "privileged"]:
score += 10
return min(score, 100) # Cap at 100Integrating Enrichment into SIEM and SOAR
Alert enrichment should not be a standalone process. It must be integrated into detection, analysis, and response workflows across the SOC stack.
Within SIEM
Enrichment can be applied during data ingestion or post-correlation. Many modern SIEMs offer plugins or APIs for enrichment services — or embed it natively. Enriched alerts improve search, correlation, and dashboard fidelity.
- Real-time enrichment during log ingestion
- Post-processing enrichment for correlation rules
- API integrations with threat intelligence platforms
- Custom enrichment plugins for organization-specific data
- Automated tagging and classification based on enriched data
Within SOAR
SOAR platforms automate enrichment steps:
- Querying asset inventories
- Pulling user context from IAM
- Fetching TI indicators from feeds
- Attaching historical incident tickets
- Calculating risk scores and priority levels
By pre-enriching alerts, SOARs reduce the investigative burden and speed up playbook execution.
# Example SOAR enrichment workflow
def enrich_alert(alert):
enriched_data = {}
# Asset enrichment
asset_info = cmdb_api.get_asset(alert.hostname)
enriched_data['asset_criticality'] = asset_info.tier
enriched_data['asset_owner'] = asset_info.owner
# User enrichment
user_info = ldap_api.get_user(alert.username)
enriched_data['user_department'] = user_info.department
enriched_data['user_privileges'] = user_info.groups
# Threat intelligence enrichment
if alert.src_ip:
ti_results = threat_intel_api.lookup_ip(alert.src_ip)
enriched_data['threat_score'] = ti_results.reputation_score
enriched_data['threat_categories'] = ti_results.categories
# Historical context
similar_alerts = siem_api.search_similar(alert, days=30)
enriched_data['historical_frequency'] = len(similar_alerts)
return {**alert.__dict__, **enriched_data}Challenges and Considerations
Despite its value, enrichment presents some challenges:
- Data Quality: Internal sources (CMDBs, user directories) must be accurate and up to date
- Latency: Real-time enrichment must balance thoroughness with performance
- Cost: High-volume enrichment against premium threat feeds can incur licensing costs
- Complexity: Orchestrating multiple enrichment sources requires well-maintained integrations and monitoring
- Privacy: Enrichment processes must comply with data protection regulations
- Scalability: Enrichment systems must handle peak alert volumes without degradation
However, these challenges are manageable — and far outweighed by the benefits of faster, more accurate decisions.

A well-designed enrichment architecture balances speed, accuracy, and scalability
Best Practices for Alert Enrichment
To maximize the effectiveness of alert enrichment, organizations should follow these best practices:
- Maintain high-quality, up-to-date internal data sources
- Implement tiered enrichment based on alert priority and volume
- Use caching to improve performance for frequently accessed data
- Establish SLAs for enrichment latency based on alert criticality
- Regularly audit and validate enrichment data sources
- Implement fallback mechanisms for when enrichment sources are unavailable
- Monitor enrichment coverage and effectiveness metrics
The Future of Alert Enrichment
As security environments continue to evolve, alert enrichment is becoming more sophisticated. Machine learning models can now predict the relevance of enrichment data, while natural language processing can extract context from unstructured sources like incident reports and security blogs.
The integration of large language models (LLMs) is particularly promising, as they can synthesize multiple enrichment sources into coherent, human-readable summaries that provide both technical details and business context.
Conclusion
Alert enrichment is not optional in modern SOCs. It is foundational. Without context, alerts are just noise — and noise leads to fatigue, mistakes, and missed threats. With context, alerts become knowledge — precise, actionable, and prioritized.
As security teams continue to battle alert volume and complexity, enrichment stands out as the catalyst for transformation. When combined with ML, LLMs, and automation, it creates a modern SOC capable of understanding, not just reacting.
Because in security, seeing is not enough. Understanding is everything.