LLMs for Alert Context Understanding: Unlocking Intelligence in the SOC

Security Operations Centers (SOCs) are the front lines of cyber defense, tasked with monitoring, analyzing, and responding to a constant barrage of security alerts. However, the sheer volume and complexity of these alerts often overwhelm analysts, leading to alert fatigue, missed threats, and delayed response times. The challenge lies in transforming raw alerts into actionable intelligence, enabling analysts to quickly understand the context, severity, and potential impact of each incident.
The Challenge: Deciphering Alert Context
Consider a typical security alert: 'Suspicious process execution detected on endpoint.' While this alert signals a potential issue, it lacks the context needed for effective triage. Analysts must manually investigate the process, user, affected system, and related events to determine if it represents a genuine threat.
Without context, analysts face questions like:
- What process was executed?
- Who initiated the process?
- What system is affected?
- Are there any related alerts or events?
- Is this behavior normal for this user or system?
Answering these questions requires significant time and effort, especially when dealing with thousands of alerts daily. This is where Large Language Models (LLMs) come into play.
What are Large Language Models (LLMs)?
Large Language Models (LLMs) are advanced artificial intelligence models trained on massive datasets of text and code. They possess a remarkable ability to understand, generate, and manipulate natural language, enabling them to perform tasks such as text summarization, entity extraction, and intent detection with unprecedented accuracy.
In the context of security operations, LLMs can be leveraged to analyze security alerts, extract relevant information, and provide analysts with a clear understanding of the incident's context.
Use Cases: LLMs in the SOC
Alert Summarization
LLMs can automatically summarize lengthy and complex security alerts, providing analysts with a concise overview of the key findings. This reduces the time required to understand the alert and prioritize investigations.
Original Alert: "Multiple failed login attempts detected from IP address 192.168.1.100 targeting user 'admin' on server 'web-server-01' between 03:00 and 03:30 UTC."
LLM Summary: "Brute-force attack detected targeting the 'admin' account on 'web-server-01' from IP 192.168.1.100."
Entity Extraction
LLMs can identify and extract key entities from security alerts, such as IP addresses, usernames, hostnames, file paths, and vulnerability identifiers. This information can be used to enrich alerts with additional context and facilitate investigations.
Original Alert: "Malicious file 'evil.exe' detected in user 'john.doe's downloads folder."
LLM Entities:
- File: evil.exe
- User: john.doe
- Path: /home/john.doe/downloads
Intent Detection
LLMs can analyze the language used in security alerts to infer the intent behind the activity. For example, an LLM can determine if a user is attempting to exfiltrate data, escalate privileges, or execute malicious code.
Original Alert: "User 'jane.doe' executed command 'sudo su' on server 'db-server-01'."
LLM Intent: "Privilege escalation attempt."
MITRE ATT&CK Mapping
LLMs can map security alerts to the MITRE ATT&CK framework, providing analysts with a structured understanding of the attacker's tactics, techniques, and procedures (TTPs). This enables analysts to quickly identify the stage of an attack and implement appropriate countermeasures.
Original Alert: "PowerShell script executed to disable Windows Defender."
LLM MITRE ATT&CK Mapping:
- Tactic: Defense Evasion
- Technique: Impair Defenses (T1562)
Playbook Generation
Based on the alert context and MITRE ATT&CK mapping, LLMs can suggest appropriate incident response playbooks, guiding analysts through the steps required to contain and remediate the threat. This automates the initial stages of incident response and ensures consistent handling of security incidents.
LLM Playbook Suggestion:
"Based on the detected brute-force attack, execute the 'Brute-Force Attack Response' playbook, which includes steps such as blocking the source IP, resetting the user's password, and reviewing audit logs."

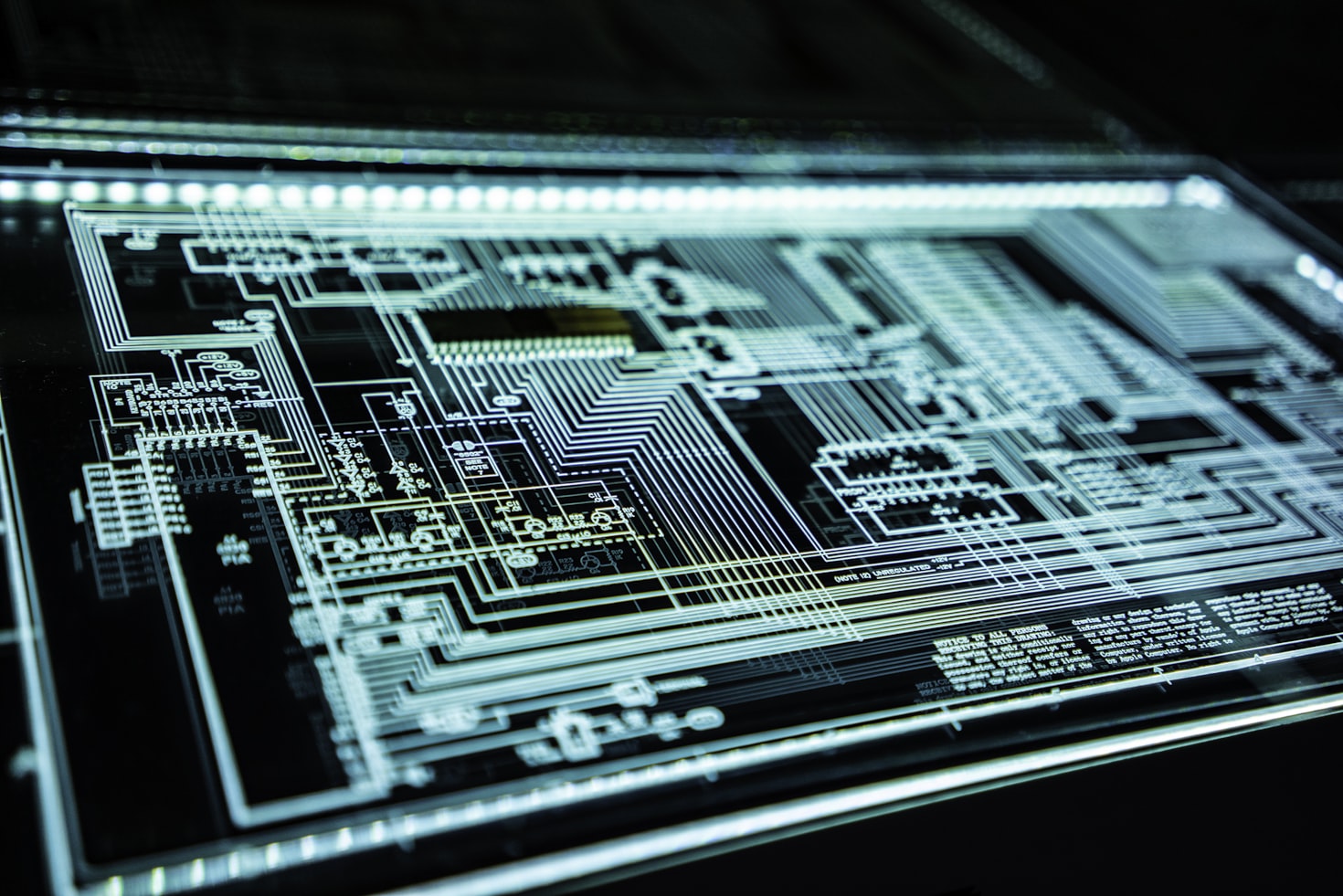
LLMs transform raw alerts into actionable intelligence, streamlining SOC operations
How LLMs Work with Real Alerts: A Workflow
Here's a typical workflow of how LLMs can be integrated into a SOC:
- Alert Ingestion: Security alerts from various sources (SIEM, EDR, etc.) are ingested into the LLM-powered system.
- Contextualization: The LLM analyzes the alert, extracts relevant entities, and enriches it with additional context from threat intelligence feeds, asset inventories, and user databases.
- Intent Detection & MITRE ATT&CK Mapping: The LLM infers the intent behind the activity and maps it to the MITRE ATT&CK framework.
- Playbook Suggestion: Based on the alert context and MITRE ATT&CK mapping, the LLM suggests an appropriate incident response playbook.
- Analyst Review: The analyst reviews the enriched alert, LLM's analysis, and playbook suggestion, making any necessary adjustments.
- Automated Response: The analyst approves the playbook, and the system automatically executes the steps required to contain and remediate the threat.
Strengths of LLMs in Alert Management
- Improved Alert Understanding: LLMs provide analysts with a clear and concise understanding of the context, severity, and potential impact of security alerts.
- Reduced Alert Fatigue: By automating the initial stages of alert triage, LLMs reduce the burden on analysts and prevent alert fatigue.
- Faster Response Times: LLMs enable analysts to respond to security incidents more quickly and effectively.
- Enhanced Threat Detection: LLMs can identify subtle patterns and anomalies that might be missed by traditional security tools.
- Consistent Incident Handling: LLMs ensure consistent handling of security incidents by suggesting appropriate incident response playbooks.
Limitations and Cautions
While LLMs offer significant benefits, it's crucial to acknowledge their limitations:
- Data Dependency: LLMs require large amounts of high-quality data to train effectively. The accuracy of the LLM's analysis depends on the quality and completeness of the training data.
- Bias: LLMs can inherit biases from the training data, leading to inaccurate or unfair analysis. It's essential to carefully evaluate and mitigate potential biases.
- Explainability: LLMs can be black boxes, making it difficult to understand why they made a particular decision. This lack of explainability can be a concern in regulated industries.
- Security Risks: LLMs themselves can be vulnerable to attacks, such as prompt injection and adversarial examples. It's essential to implement security measures to protect LLMs from these threats.
Future Outlook
The use of LLMs in security operations is still in its early stages, but the potential is enormous. As LLMs continue to evolve, we can expect to see even more sophisticated applications, such as automated threat hunting, proactive vulnerability discovery, and personalized security awareness training.
The integration of LLMs with other AI technologies, such as machine learning and deep learning, will further enhance their capabilities and enable them to address even more complex security challenges.
Conclusion
Large Language Models are poised to revolutionize Security Operations Centers by transforming raw alerts into actionable intelligence. By automating alert summarization, entity extraction, intent detection, and playbook generation, LLMs empower analysts to respond to security incidents more quickly, effectively, and consistently.
While challenges remain, the benefits of LLMs in alert management are undeniable. As organizations continue to grapple with the ever-increasing volume and complexity of security alerts, LLMs offer a path to unlocking intelligence in the SOC and strengthening cyber defenses.